The InterPlanetary File System (IPFS) is a content-addressed peer-to-peer file sharing network from Protocol Labs being exploited by cybercriminals to host phishing sites and other malicious content. Often associated with the web 3.0 movement, it allows its users to upload, share, and download files across a distributed worldwide network.
Gateways make IPFS accessible to the broader public, allowing pages powered by IPFS to be visited in traditional web browsers and shared with potential victims. Netcraft first detected cyber attacks using IPFS in 2016, and now detects and blocks hundreds of attacks using IPFS gateways every day.
This blog post describes what IPFS is and how it works, how and why it is used by cybercriminals, and what Netcraft is doing to block and disrupt attacks that leverage the IPFS network.
What is IPFS?
IPFS is a decentralized storage and delivery network technology. Unlike the traditional web, where most content is hosted on dedicated servers, IPFS is peer-to-peer, which means there is no single server providing each page. Instead, content is accessed via any peer (also known as a node) that has a copy of the content, with little distinction between servers and users.
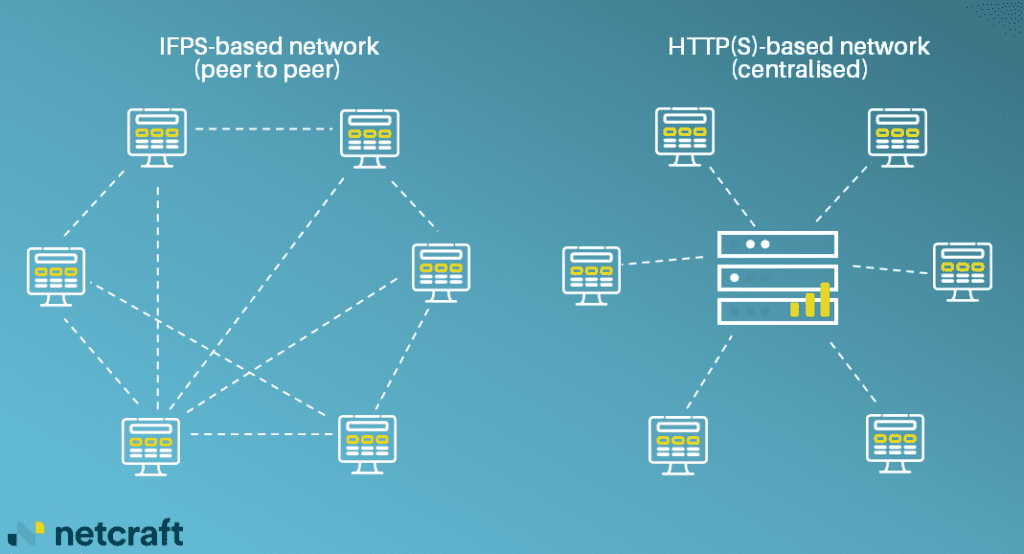
The decentralized structure allows users to host or share content with increased availability and resilience. Filecoin, a cryptocurrency which builds upon IPFS to incentivize node operators to host content, is significantly cheaper than using cloud storage services like Amazon S3 at the time of writing. Eliminating the need for a single server also means content can be accessed from nodes hosted in a wide variety of locations in multiple jurisdictions—improving availability but making it more difficult to remove content.
How does IPFS manage content?
The traditional web is location-addressed: URLs, such as https://www.net
[…]
Content was cut in order to protect the source.Please visit the source for the rest of the article.
Read the original article: